
News
Zafran Team
Zafran Announces Strategic Investment from Amex Ventures
This is the default text value
Zafran's agentic platform proves what attackers can exploit in your environment, then mobilizes your existing defenses to stop them.
Zafran is for security teams buried in vulnerabilities and manual work.
The AI-Native Exposure Management Platform

Turn fragmented scanner output into one actionable view.
Zafran brings vulnerability findings together across your existing tools, creating a unified view of exposure across the hybrid enterprise.
Know what is actually exploitable.
Zafran applies your unique risk context to reveal which vulnerabilities are truly exploitable in your environment.
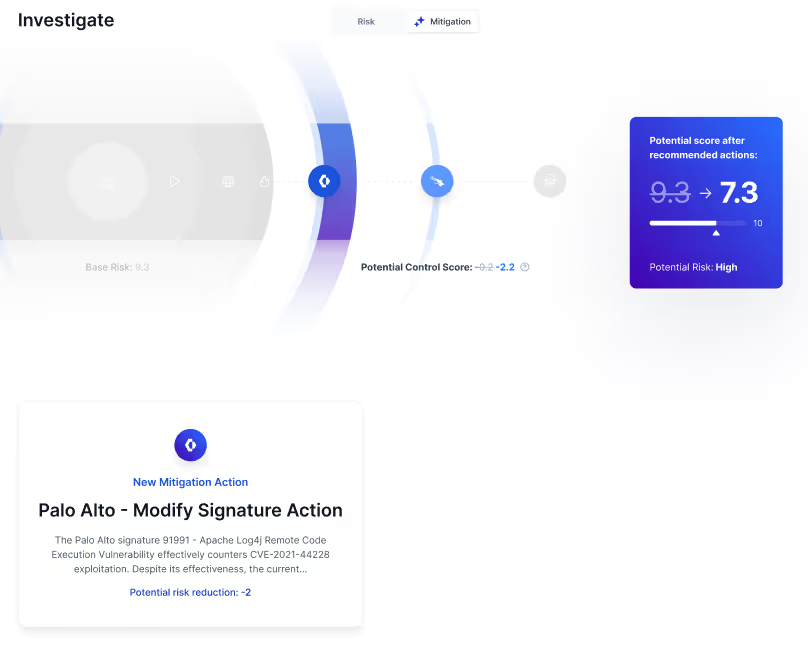
Reduce risk now, without waiting on patch cycles.
Zafran uses your existing security controls to show how to quickly reduce exploitability across your environment.
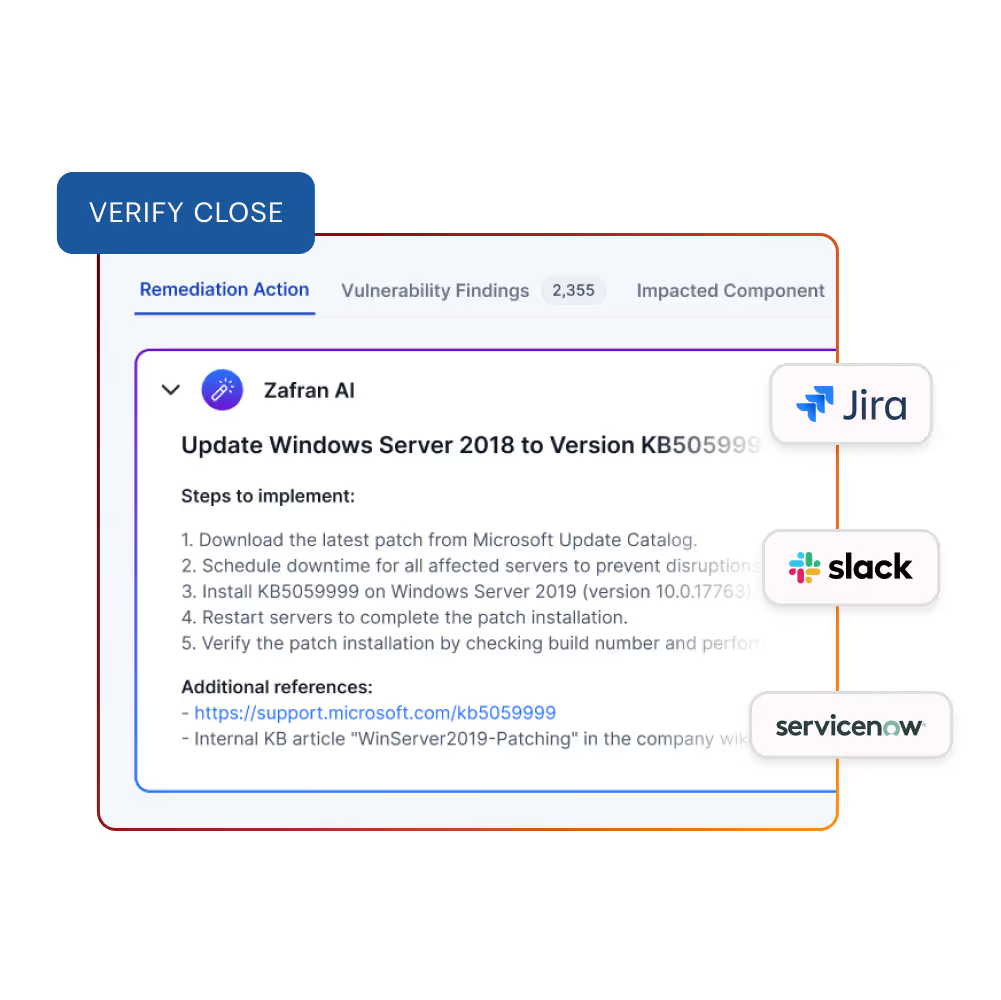
Turn vulnerability insights into focused remediation action.
RemOps uses generative AI to consolidate overlapping remediation tasks, create a clear get-well plan, and route work to the right owners through your existing ticketing platforms.
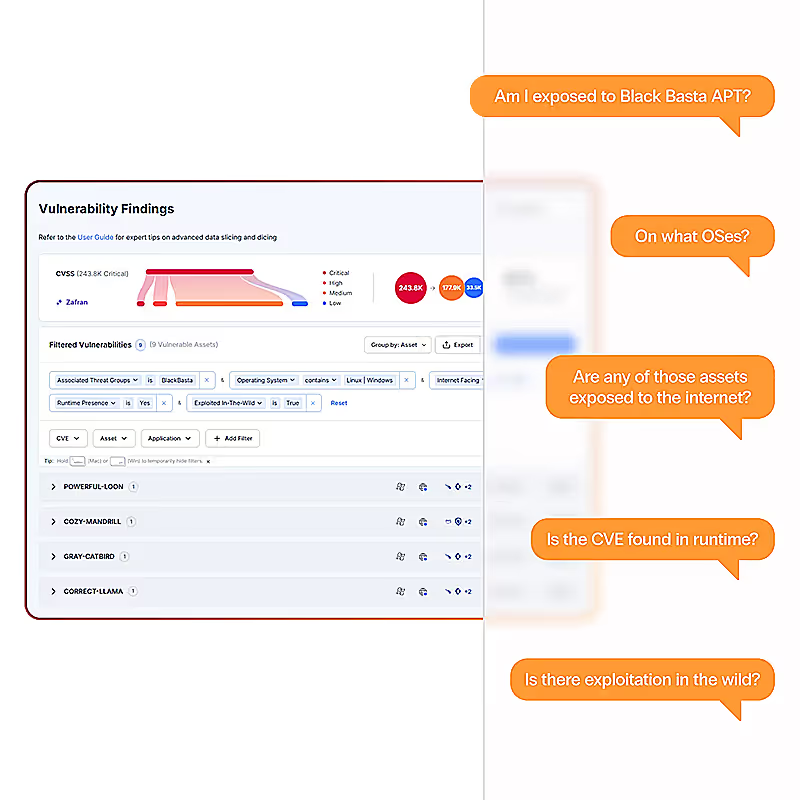
Answer “Are we exposed?” with precision.
Zafran helps security teams proactively hunt for exposures tied to new CVEs, zero-days, threat actors, and control gaps across the hybrid enterprise.

The Context Layer to Power Autonomous Actions
Exposure Graph Continuously Maps Exposures to Existing Security Controls
00:00
/
00:00
Autonomous AI agents for your entire vulnerability management lifecycle

See Zafran in Action
Prioritize and fix what is truly exploitable using risk context from your existing security tools